Hi All,
Greetings from India !!
Well, I’ve been using Openfire/Spark since March’14 for my organization and user adoption today is par our expectation. Well observing the adoption of application, we decided to focus on security aspects. Following that we bought a 2048-bit SSL certificate from CA(Certificate Authority), that is entrust.
We purchased certificate in April’14 and working on the same since then but didn’t get any success on it.
Please look upon the steps(respective commands) we followed to configure SSL on Openfire.
- Generated keystore using this command.
keytool -genkey -alias smartssl -keysize 2048 -keyalg RSA -keystore D:\SSL\ssl.keystore
- Generate Certificate Signing Request and sent to CA
keytool -certreq -keyalg RSA -alias smartssl -file D:\SSL\certreq.csr -keystore D:\SSL\ssl.keystore
-
Post receiving a bundle (containing four files as listed below) from CA. we installed all certificates in respective order except ROOT certificate.
-
L1Kroot.txt
- ignored.
- L1Kchainroot.txt
keytool -import -alias smartchatchainroot -keystore “D:\SSL\ssl.keystore” -trustcacerts -file “D:\SSL\L1Kchainroot.cer”
- L1Kchain.txt
keytool -import -alias smartchatchain -keystore “D:\SSL\ssl.keystore” -trustcacerts -file “D:\SSL\L1Kchain.cer”
- entrustcert.crt
keytool -import -alias smartchatserver -keystore “D:\SSL\ssl.keystore” -trustcacerts -file “D:\SSL\entrustcert.crt”
5 Inserted following properties in System Properties
xmpp.socket.ssl.active - true
xmpp.socket.ssl.keypass - rcom123
xmpp.socket.ssl.keystore - resources/security/ssl.keystore
xmpp.socket.ssl.port - 5223
xmpp.socket.ssl.storeType - JKS
Note: Didn’t add trust store as seems it is not required.
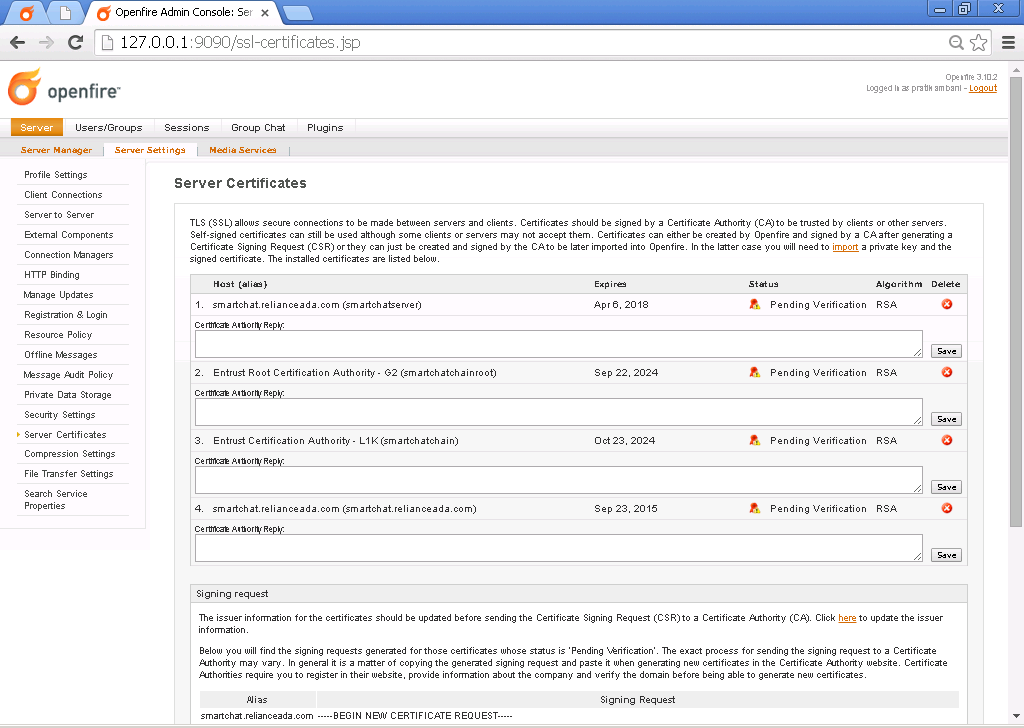
After adding following properties SSL Certificate page in Admin console looks like this.
Thanks and Regards,
Kitarp